Navigating a Shifting World
Conventional security
tools have not
kept pace

The nature of business and work have changed

A trusted partner to monitor and analyze organization's security & operations

Our Information Security Solutions ensure business continuity and reduce business damage by preventing and minimizing the impact of security incidents. Our Endpoint and Hybrid Security strategy helps enterprises protect users and critical assets with multilayered security.
A security operations center (SOC) is a facility that houses an information security team responsible for monitoring and analyzing an organization’s security posture on an ongoing basis.
Resemble Systems Next generation security operations and response services along with a deep portfolio of consulting, recommendation and managed services, can help organizations build a transformation strategy and roadmap to implement the next generation of security operations.
Protect your most valuable data in the cloud and on-premises with Resemble Systems security-first approach. Resemble Systems has decades of experience securing data and applications. Designed to protect customer workloads with a security-first approach across computer, network, and storage. Resemble Systems is complemented by essential security services to provide the required levels of security for your most business-critical workloads.


Our Information Security Solutions ensure business continuity and reduce business damage by preventing and minimizing the impact of security incidents. Our Endpoint and Hybrid Security strategy helps enterprises protect users and critical assets with multilayered security.
A security operations center (SOC) is a facility that houses an information security team responsible for monitoring and analyzing an organization’s security posture on an ongoing basis.
Resemble Systems Next generation security operations and response services along with a deep portfolio of consulting, recommendation and managed services, can help organizations build a transformation strategy and roadmap to implement the next generation of security operations.
Protect your most valuable data in the cloud and on-premises with Resemble Systems security-first approach. Resemble Systems has decades of experience securing data and applications. Designed to protect customer workloads with a security-first approach across computer, network, and storage. Resemble Systems is complemented by essential security services to provide the required levels of security for your most business-critical workloads.

Our Information Security Solutions ensure business continuity and reduce business damage by preventing and minimizing the impact of security incidents. Our Endpoint and Hybrid Security strategy helps enterprises protect users and critical assets with multilayered security.
A security operations center (SOC) is a facility that houses an information security team responsible for monitoring and analyzing an organization’s security posture on an ongoing basis.
Resemble Systems Next generation security operations and response services along with a deep portfolio of consulting, recommendation and managed services, can help organizations build a transformation strategy and roadmap to implement the next generation of security operations.

Securing cloud environments against unauthorized use/access

Artificial intelligence fused with critical endpoint technologies.
Safeguard your email with our industry-leading threat and anti-spam protection.

Uncover, prioritize, investigate & remediate complex attacks across endpoint email network.

Designed to secure corporate data on employees' mobile devices.

Identity and access management for the cloud.

Securing cloud environments against unauthorized use/access.

Artificial intelligence fused with critical endpoint technologies.
Safeguard your email with our industry-leading threat and anti-spam protection.

Uncover, prioritize, investigate & remediate complex attacks across endpoint email network.

Designed to secure corporate data on employees' mobile devices.

Identity and access management for the cloud.

Protect your most valuable data in the cloud and on-premises with Resemble Systems security-first approach. Resemble Systems has decades of experience securing data and applications. Designed to protect customer workloads with a security-first approach across computer, network, and storage. Resemble Systems is complemented by essential security services to provide the required levels of security for your most business-critical workloads.

Securing cloud environments against unauthorized use/access.

Artificial intelligence fused with critical endpoint technologies.
Safeguard your email with our industry-leading threat and anti-spam protection.

Uncover, prioritize, investigate & remediate complex attacks across endpoint email network.

Designed to secure corporate data on employees' mobile devices.

Identity and access management for the cloud.






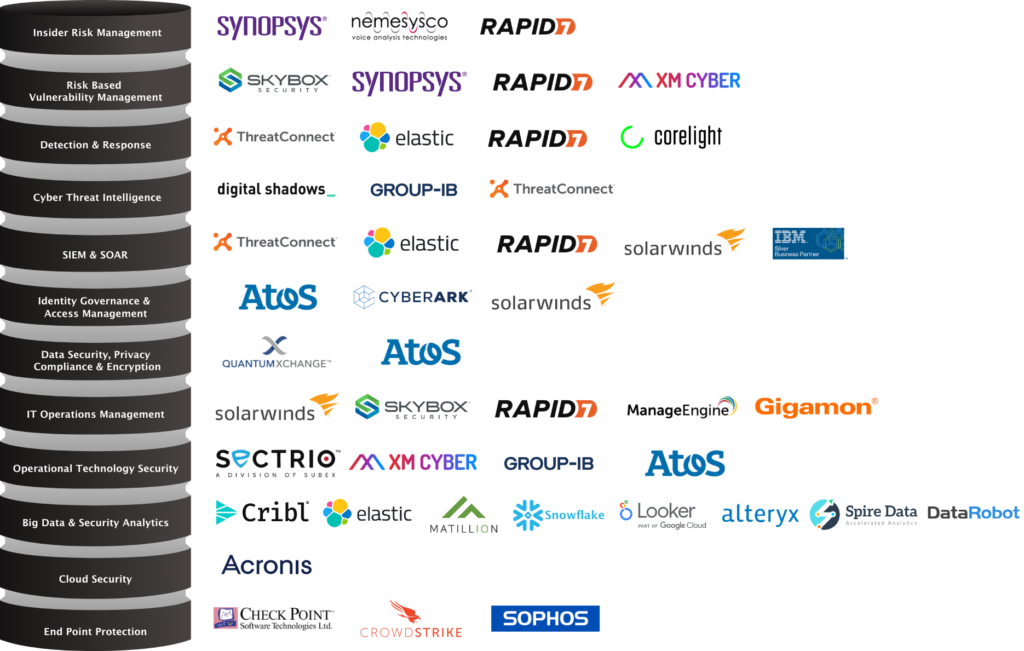
Technologies
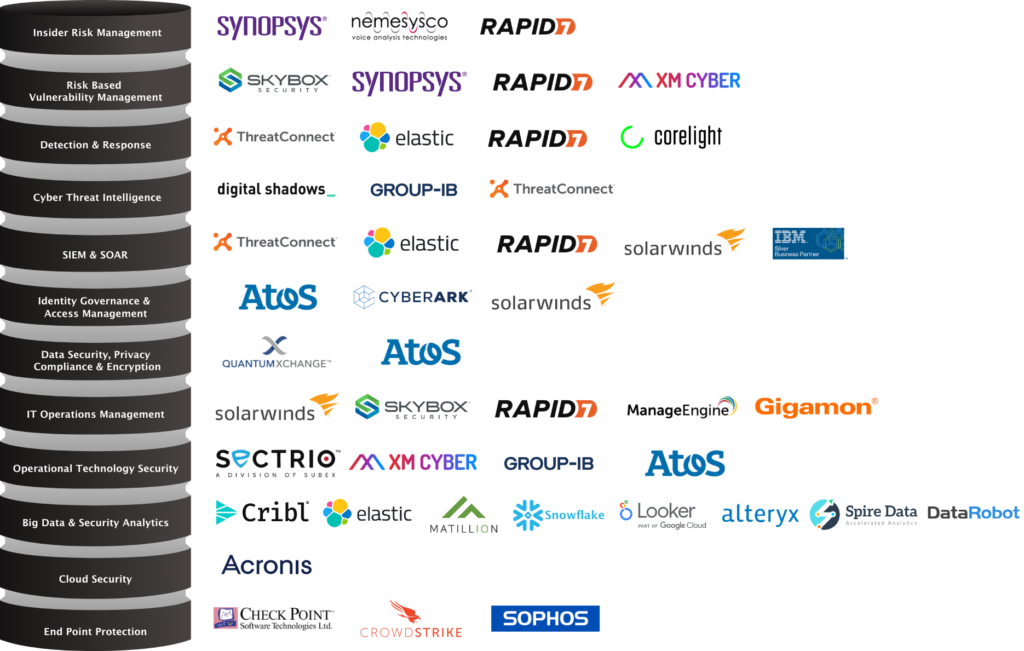



































Technologies
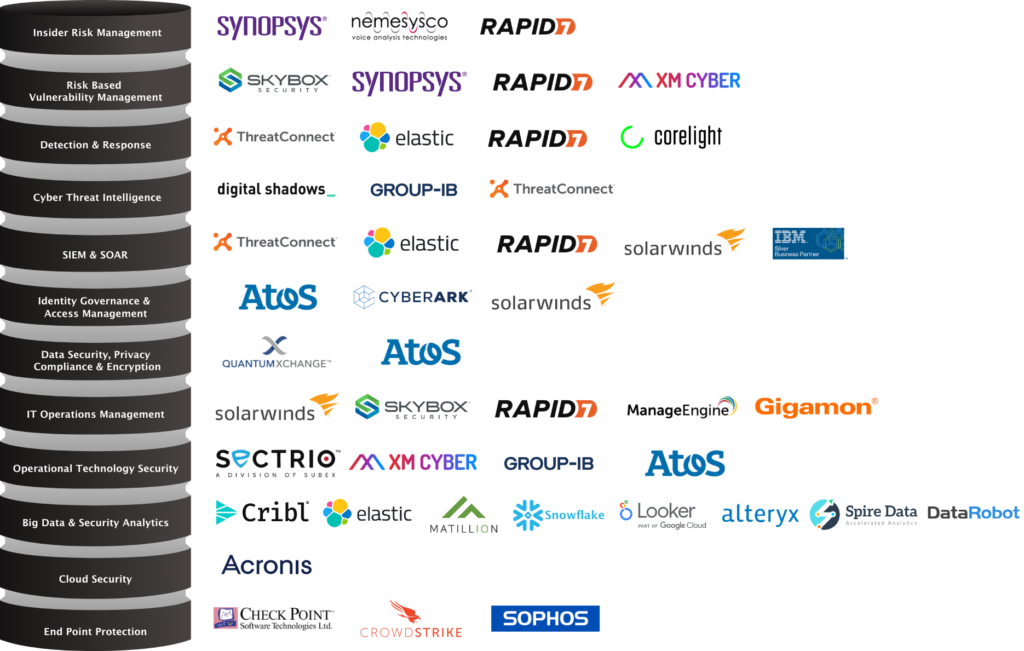



































Technologies





































Q&A
A security operations centre is a centralized unit that deals with security issues on an organizational and technical level. It comprises the three building blocks for managing and enhancing an organization's security posture: people, processes, and technology.
The function of the security operations centre (SOC) is to monitor, prevent, detect, investigate, and respond to cyber threats around the clock. SOC teams are charged with monitoring and protecting the organization's assets including intellectual property, personnel data, business systems, and brand integrity.
Q&A
A cyber security operations centre is a centralized unit that deals with security issues on an organizational and technical level. It comprises the three building blocks for managing and enhancing an organization's security posture: people, processes, and technology.
The function of the security operations centre (SOC) is to monitor, prevent, detect, investigate, and respond to cyber threats around the clock. SOC teams are charged with monitoring and protecting the organization's assets including intellectual property, personnel data, business systems, and brand integrity.
Q&A
A cyber security operations centre is a centralized unit that deals with security issues on an organizational and technical level. It comprises the three building blocks for managing and enhancing an organization's security posture: people, processes, and technology.
The function of the security operations centre (SOC) is to monitor, prevent, detect, investigate, and respond to cyber threats around the clock. SOC teams are charged with monitoring and protecting the organization's assets including intellectual property, personnel data, business systems, and brand integrity.
Copyright © 2020- 2021 Resemblesystems.com, All rights reserved.
Copyright © 2020- 2021 Resemblesystems.com, All rights reserved.
Copyright © 2020- 2021 Resemblesystems.com, All rights reserved.